On our new Office Web Apps installation, I was seeing errors in the event viewer repeating every few minutes such as
Faulting application name: SandboxHost.exe, version: 15.0.4502.1000, time stamp: 0x512d262b Faulting module name: KERNELBASE.dll, version: 6.3.9600.17278, time stamp: 0x53eebf2e
I applied each of the April, May, June and July Cumulative updates, and each time hoped that they would solve the problem. They didn’t.
The key here was taking a closer look at the ULS logs, which have additional detail. This log can be found (default) at C:\ProgramData\Microsoft\OfficeWebApps\Data\Logs\ULS
I found a corresponding entry which provided the hint to the real problem
Failed to launch sandbox process, SE_ASSIGNPRIMARYTOKEN_NAME and SE_INCREASE_QUOTA_NAME privileges are required
This error is typically seen in Sharepoint installations, but the root cause is the same. The service account which is running doesn’t have the necessary permissions.
Office Web Apps uses the LocalSystem account by default. I had changed this to a specialized service account which had permissions into Sharepoint Content databases, in order to isolate a different problem related to Web Apps not working on Sharepoint personal sites.
As a result, it didn’t have the required permissions.
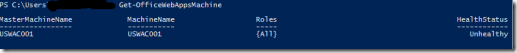
Utilizing this article at Al’s Tech Tips, I made the appropriate changes to the Local Security Policy. Whereas his article talks about the service account running the Sharepoint User Code Host, the one we are concerned about with Office Web Apps Server is Office Web Apps (WACSM)